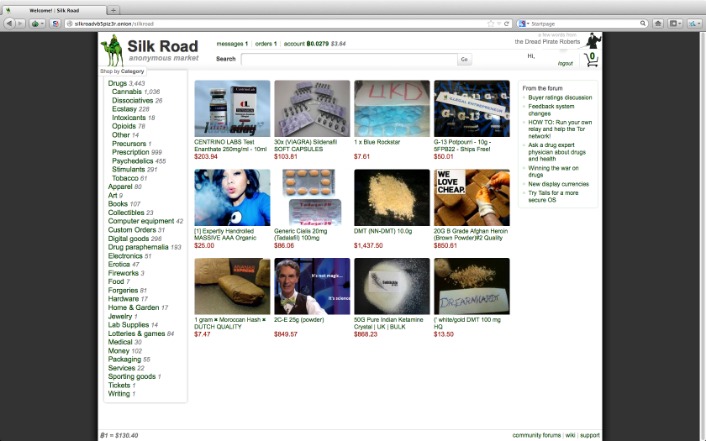
Regular dark web visitors know that it’s possible to exploit the sketchy reputation of the space and the services offered. And with many unfamiliar-looking sites on the dark web, it’s harder to distinguish safe websites from shady ones, and easier to fall victim. The subreddit r/deepweb is a good starting point for asking more experienced users about how to search the dark web and deep web for the content you want. Surface web search engines can’t access the darknet, but specialized dark web search engines can help you find what you’re looking for. As always, protect yourself from online threats with mobile Android security or iOS security software.
The term "dark web" conjures images of a hidden digital underworld, a place shrouded in mystery and often associated with illicit activity. In reality, it is a small, intentionally concealed portion of the deep web, which itself is the vast collection of online content not indexed by standard search engines. To access the dark web, one must use specific software and configurations, a process that emphasizes anonymity but also requires significant caution.
- As for the dark web, it’s intentionally hidden, encrypted, and made anonymous.
- The history of the Dark Web reflects the intricate interplay between technology, privacy concerns, and the ever-evolving landscape of online activities.
- Despite the dark web’s anonymity, users still need tools to navigate its vast and often confusing landscape.
- DeepSearch is an open-source search engine for serious ventures into the Tor network's onion space.
- If you value quality over quantity in search results, give DeepSearch a try for a cleaner dark web search experience.
These services monitor the dark web for a variety of purposes, including looking for stolen business and personal credentials, domains, IP addresses and email addresses. Many companies have turned to dark web monitoring services to protect themselves from the risks posed by dark web credential exposure. It can be challenging to keep track of all your dark web login information, and using the same password for multiple sites is a significant security risk. It is simply a different section of the internet that is harder to access and less regulated. Once you are connected, you will be able to access the dark web. The Tor browser uses the Tor network to bounce your traffic through multiple servers around the world, making it virtually impossible for anyone to track your activity.
Access The Dark Web
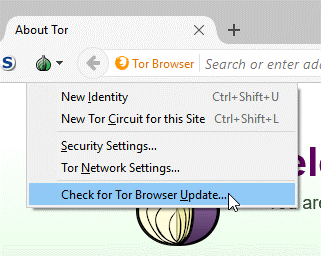
To successfully access the dark web, standard browsers like Chrome or Firefox are ineffective. The primary gateway is the Tor network, which routes internet traffic through multiple layers of encryption and a series of volunteer-run servers. This process obscures a user's location and usage from surveillance. Downloading the Tor Browser is the fundamental first step for anyone aiming to access the dark web safely.
Navigating and Understanding the Environment
Once connected via Tor, users can access the dark web sites, known as Tor hidden services. These addresses end in ".onion" and are not accessible through conventional means. Navigation is challenging, as there is no central directory. While some wikis and forums index links, extreme discretion is required. The act to access the dark web places the user in an ecosystem where both legitimate privacy advocates and criminal entities operate.
Critical Security Precautions
Merely using Tor does not guarantee anonymity. To securely access the dark web, additional measures are non-negotiable. A comprehensive VPN, updated firewall, and disabling scripts within the Tor Browser are essential. Users must never share personal information or use familiar credentials. The decision to access the dark web must be accompanied by a commitment to operational security to mitigate risks like malware or phishing scams.
Ultimately, the tools that enable one to access the dark web are designed for privacy, a principle vital for journalists, activists, and citizens under oppressive regimes. However, this same privacy attracts illegal commerce and communication. Therefore, the intent behind the choice to access the dark web defines the experience, separating lawful pursuit of confidentiality from dangerous or illegal ventures.