The internet most people experience is a surface layer, a fraction of the whole. Beneath it lies the deep web, and within that, a smaller, intentionally hidden segment: the dark web. Access to the dark web is not achieved through standard browsers or search engines. It requires specific tools and knowledge, creating a digital space defined by both its technical architecture and its controversial reputation.
The dark web hosts a myriad of activities, spanning from wholly legitimate to highly illegal. Threat actors often use the dark web to conduct their operations anonymously, making it a significant concern for cybersecurity professionals and law enforcement agencies. Listen to expert conversations and insights on cybersecurity trends, threats and best practices. Browse our webinar library to learn about the latest threats and issues in cybersecurity. Stay up to date on emerging cyber threats with insights from our industry-leading threat research team. Learn how organizations use Proofpoint to strengthen their cybersecurity, protect their data, and reduce risk.
- Through a method known as onion routing, data is encrypted and then ferried across numerous nodes which provide various layers of anonymity and protection.
- The deep web comprises non-indexed sites that are not accessible via standard search engines.
- Safe exploration is possible when users stick to verified resources, avoid downloads, and treat every unknown page with skepticism.
- It can simply be a dangerous proposition to peruse the Dark Web and engage with whoever you may meet, especially if it means revealing any personal data.
- Silk Road was one of the first dark web marketplaces that emerged in 2011 and has allowed for the trading of illegal drugs, weapons and identity fraud resources.
So with all this illegal activity taking place on to the dark web, is it really okay to log on? It also sells more than the illicit substances it's often known for, contraband can include stolen data, illegal firearms and exploitation material. For investigators, it can hold crucial information that would otherwise be inaccessible. In many countries, the dark web allows demonstrators to subvert authoritarian regimes and provides a free and open internet model that can evade censorship and provide privacy. Perhaps best known for its association with illicit activities, the dark web has become infamous for its role in the illegal drug trade. Investigators should use non-attributable, isolated browsing with full auditing to reduce legal, security, and privacy risk.
- This level of anonymity makes the dark web a haven for illegal activities, such as drug trafficking and various types of cybercrime.
- Fraud and scams run rampant on the dark web, including offers too good to be true and fake services requiring upfront payment.
- Outdated browsers miss critical updates that fix vulnerabilities exploited on hidden networks.
- In 2015 it was announced that Interpol now offers a dedicated dark web training program featuring technical information on Tor, cybersecurity and simulated darknet market takedowns.
- Almost 99% of web content is thought to evade search engines.
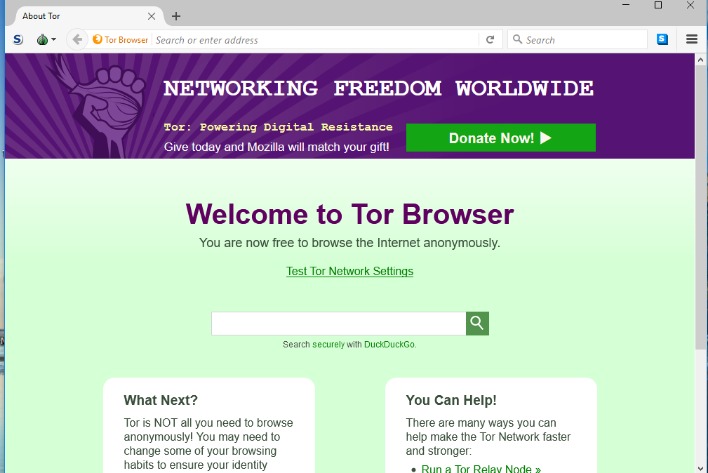
Access To Dark Web
Gaining access to the dark web fundamentally relies on overlay networks that operate on top of the existing internet. The most well-known gateway is The Onion Router, or Tor. The Tor browser is the primary tool for this purpose, routing user traffic through multiple encrypted layers to anonymize both the source and the destination. This process, while central to access to the dark web, is slower than conventional browsing.
The Role of Anonymity
This layered encryption is the core feature enabling access to the dark web. It protects users' identities and locations, which is a double-edged sword. This technology is vital for political dissidents, whistleblowers, and journalists operating under oppressive regimes. However, the same anonymity also shields illegal marketplaces and other illicit activities, which often dominate the public perception of these spaces.
Navigating the Hidden Terrain
Once access to the dark web is established via Tor, navigation presents its own challenges. Websites here use .onion addresses, which are long strings of characters. There are no central directories like Google. Users rely on curated lists, forums, or word-of-mouth to find links. This obscurity is by design, making the process of finding reliable and safe resources a significant hurdle in one's access to the dark web.
Ultimately, access to the dark web represents a specific technological capability with profound implications. It is a tool for privacy and free speech as much as it is a conduit for crime. Understanding the mechanisms behind this access is crucial for any informed discussion about online freedom, security, and the future of the internet's hidden layers.