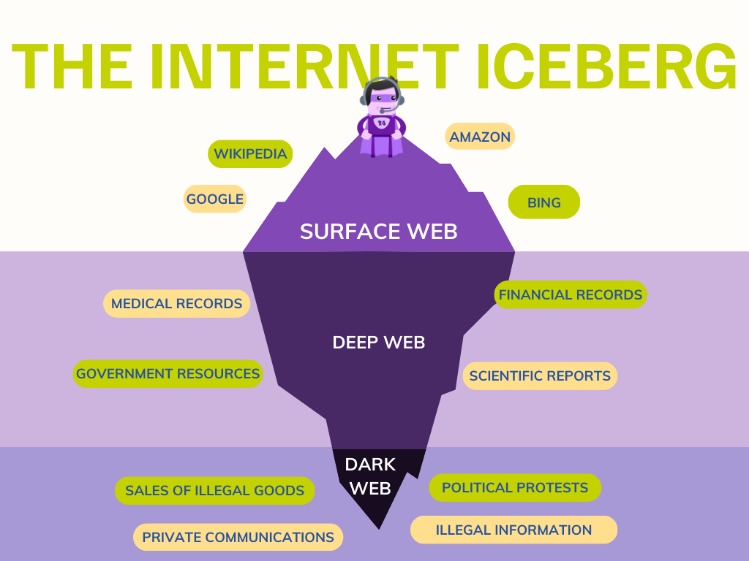
Beneath the familiar surface of the internet lies a vast, unindexed network known as the dark web. Access to the dark web is often shrouded in mystery and misconception, associated primarily with illicit marketplaces. However, it also serves as a critical tool for whistleblowers, journalists, and activists operating under oppressive regimes. Gaining this access requires specific tools and knowledge, fundamentally separating it from everyday browsing.
Access To The Dark Web
Darknets and Dark Web sites are encrypted, peer-to-peer networks that are only accessible via certain tools. Engaging in illegal activities—like buying drugs, trafficking stolen data, or distributing harmful content—is absolutely against the law. The history of the Dark Web is intricately tied to the development of internet technology and the ongoing pursuit of online anonymity. Tools such as Ahmia, Torch, and Haystak index hidden services, offering keyword search and content filtering.
The dark web is full of malicious actors, cybercriminals, and other people who are looking to prey on curious but unprepared dark web browsers. This process, though, can often involve accessing the dark web for research into the most current malware on the market. That being said, the anonymity offered by the dark web is the perfect breeding ground for criminals from all walks of life and users are advised to browse with extreme caution. An easy way to think about this is if you need a username and password to access it, it’s a part of the deep web.
Unlike the open web, access to the dark web is not achieved through standard browsers like Chrome or Firefox. It relies on overlay networks that use complex encryption and routing protocols to anonymize both the user and the sites visited. The most common gateway is the Tor network, which is central to understanding how this access works.
- The Deep Web contains all the web sites that web crawlers cannot index.
- Since receiving Tor Project support in 2014, Ahmia has maintained dual access points through both clearnet and onion interfaces.
- Looking for a managed attribution platform to safely access the dark web?
- When you hear the terms deep web and dark web, many people may think of dangerous places related to cybercrime.
- Useful for continuous scanning without manual searches.
How To Gain Access
The primary method for access to the dark web is the Tor Browser. It is a modified version of Firefox designed specifically to route traffic through the Tor network. This process involves:
- Downloading the Tor Browser from the official Tor Project website.
- Installing and launching the browser, which connects to the Tor network.
- Using .onion addresses, which are unique to the dark web, to visit sites.
- Law enforcement agencies don’t pay much attention to the Gray Web, so users don’t feel the need to be anonymous.
- No advanced filtering or onion-specific tools
- Practice good cybersecurity at all times and use systems that are not connected to your company network and are properly secured when communicating with cyber criminals.”
- Dark web search engines help locate leaked files and database dumps.
- Security professionals use these tools to track cybercriminal activity, uncover leaked credentials, and identify potential threats before they escalate.
Common Uses and Misconceptions
While access to the dark web is linked to illegal activities, its uses are diverse. It is crucial to separate fact from fiction.
- Privacy-Conscious Communication: Secure email services and forums for political dissidents.
- Bypassing Censorship: Accessing news sites blocked by national firewalls.
- Illicit Marketplaces: The sale of drugs, stolen data, and other illegal goods (a significant risk).
- Research and Journalism: Academics and reporters use it to contact sources anonymously.
Frequently Asked Questions (FAQs)
Is accessing the dark web illegal?
In most countries, simply gaining access to the dark web is not illegal. However, engaging in illegal activities while using it is against the law.
Does using Tor make me completely anonymous?
No. While Tor provides strong anonymity, operational security mistakes can de-anonymize users. It is a powerful tool, not an invisibility cloak.
What are the main risks?
Risks include exposure to malicious software, scams, illegal content, and potential surveillance by law enforcement targeting dark web domains.
Ultimately, access to the dark web represents a double-edged sword of digital freedom. It is a space that empowers those needing privacy for legitimate reasons but also harbors significant criminal elements. Understanding the technology, purposes, and inherent dangers is essential for anyone considering venturing into this hidden layer of the internet.