Beneath the familiar internet lies a vast, hidden landscape known as the darknet. This obscured layer of the web, inaccessible through standard browsers, is often conflated with criminal activity, yet its existence is fundamentally about privacy and anonymity. To navigate this space, one doesn't use typical web addresses; instead, access is granted through unique, complex identifiers known as onion addresses. These form the core of the adress darknet ecosystem, a gateway to a world that is both controversial and essential for many.
We actually launched it quietly as an experiment last year, shortly after publishing Inside the Firewall, an interactive news application about online media censorship in China. Readers use our interactive databases to see data that reveals a lot about themselves, such as whether their doctor receives payments from drug companies. Stay secure with DeepStrike penetration testing services.
This cybersecurity measure is often enough to cause them to give up and move on to the next target. With 2FA enabled, scammers need more than just your password to access an account. This is an additional layer of security that requires a secondary form of authentication before you can log in to an account — such as a special code sent to your phone. But they’re limited in how much of your personal information they can track — for example, they won’t tell you if your SSN or credit card information was leaked in a data breach. While most companies are legally required to send out data breach notifications to impacted customers, there are other ways to proactively see if your email was part of a recent leak. If you’ve been part of a data breach, there’s a good chance that your email can now be found on the Dark Web — but is this something you need to worry about?
Adress Darknet
- If you’re on Mac OS X, you will be prompted to optionally run several commands to have launchd start tor at login, after installing.
- Using Google to find people search databases can lead you to tools where you can conduct deep web searches on individuals.
- The operation involved the seizure of over 400 Tor website addresses – known as ".onion" addresses – as well as the servers hosting them.
- Chainalysis empowers the ecosystem with the technology to detect these activities, playing a critical role in mitigating scams like address poisoning by identifying suspicious patterns, tracing illicit fund movements, and detecting anomalies in real-time.
- In another study , Ragini Sharma et.al proposed a teacher(large networks) student(small network at edge) model using transfer learning.
The term adress darknet specifically refers to the addressing system that makes the darknet function. Unlike clear web URLs, these addresses are long strings of random letters and numbers followed by the .onion top-level domain. They are not registered with any central authority but are generated through cryptographic means, directly linking the address to the server's public key. This means the adress darknet is both a location and a proof of identity, creating a self-authenticating system where knowing the address is the only way to find the service.
How the Onion Address Works
When you enter an adress darknet into a compatible browser like Tor, your request is encrypted and routed through a series of volunteer relays. Each relay peels back a layer of encryption—hence the "onion" metaphor—to reveal the next hop. Crucially, no single relay knows both the origin and the destination. The final relay decrypts the innermost layer and connects to the .onion service. This complex routing ensures that both the user and the operator of a site can maintain strong anonymity, provided operational security is maintained.
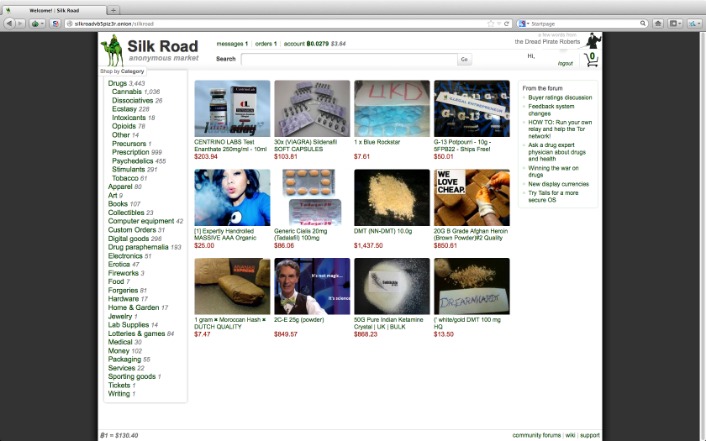
The Dual Nature of the Hidden Web
The adress darknet system enables a wide spectrum of activities. It is a vital tool for journalists, activists, and whistleblowers operating under oppressive regimes, allowing them to communicate and share information without fear of reprisal. However, the same anonymity protects illicit marketplaces and other criminal enterprises. This duality is inherent to the technology; the adress darknet does not discriminate, making it a powerful instrument for both liberation and lawbreaking.
Security Implications and Considerations
Engaging with the adress darknet carries significant risks. The anonymity that protects dissidents also shields scammers. There is no customer service or guaranteed recourse if something goes wrong. Furthermore, while the network provides anonymity, it is not inherently secure against all threats; user error can lead to exposure. Navigating this space requires extreme caution, robust security practices, and a clear understanding that the adress darknet is a neutral tool whose use is defined solely by its operator and visitor.
Ultimately, the ecosystem defined by the adress darknet represents a fundamental philosophical battleground for the digital age: the tension between absolute privacy and collective security. Its very existence challenges conventional notions of oversight and freedom on the internet, ensuring it will remain a critical, if misunderstood, component of our online world.