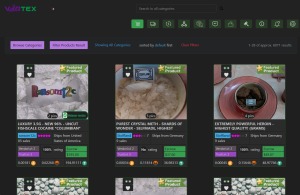
While many dark web websites, like the former black market website Silk Road, are used to facilitate criminal activity, there are also plenty of legitimate dark web websites. On the Tor network, the onion domain name reflects the fact that, like the layers of an onion, the Tor browser consists of layers of protection. Before attempting to use it, learn more about the dark web and make sure you know how to stay safe on dark web websites. In the image above, (a) is the surface web, which includes publicly visible websites like blogs, shopping sites, and news sites.
Unlike surface web crawlers, these engines rely on a combination of directory listings, user submissions, and active crawling of .onion sites. These search engines are mostly employed in the fields of research, detection work, and intelligence where access to dark web sites is an absolute necessity. This area has turned to be a dependent source for years of journalists, researchers, and privacy-centric users who trust on anonymous networks like Tor and the principle of onion routing. In contrast to websites on the surface web that anyone can visit, dark web sites are hidden in very tightly secured networks that can only be accessed by means of a dark web browser which is one of the advanced tools. As when visiting ordinary websites, stay alert to security risks on onion sites. The deep web is the part of the internet you can’t access through search engines like Google and Bing.
- Given that some hosting services may host thousands of sites, like in the case of Daniel’s hosting service, we estimate that the number of different servers is in the hundreds or low thousands.
- There are multiple documented cases of researchers, evils, and governments running exit nodes simply to capture data.
- Developers and advanced users keep it as a supplementary tool for sanity checks and behavior testing.
- The onion site is especially beneficial for people in regions with heavy censorship or restricted access to media.
- Certain online communities share and discuss Dark Web links, though it’s crucial to verify their trustworthiness, as forums may also link to malicious sites.
Beneath the surface of the familiar internet lies a parallel network, accessible only through specialized software and known for its strong emphasis on privacy and anonymity. This is the Tor network, and its hidden corners are marked by a unique addressing system: the .onion link. These are not typical web addresses; they are cryptographic identifiers that point to hidden services, offering a level of obscurity for both publishers and visitors that the clearnet cannot provide.
What Are .onion Links?
While dark web search engines are essential for accessing the dark web and monitoring potential threats to your business, they also pose their own risks. OnionLinks is not a search engine but rather a categorized directory of .onion websites. This means they search for .onion websites through automated means, but also allow users to suggest new sites, most often anonymously. We provide a secure, comprehensive, and constantly updated catalog of .onion domains to help both security researchers and privacy-conscious users navigate the Tor network safely and confidently. OnionLinkHub is the internet's premier verified directory of dark web links, onion sites, and Tor links. Housed here are “hidden services”, sites that live on the TOR network and can only be accessed from TOR.

An .onion address is a string of 56 seemingly random letters and numbers, followed by the .onion suffix. For example, a legitimate directory might look like: `duckduckgogg42xjoc72x3sjasowoarfbgcmvfimaftt6twagswzczad.onion`. This complex name is not arbitrary; it is derived from a public key and acts as both the address and the proof of identity for the hidden service. To access these sites, you must use the Tor Browser, which routes your connection through multiple encrypted layers, masking your location and the site's location.
How .onion Links Work
The process relies on Tor's onion routing protocol. When you try to visit an .onion site, your request is wrapped in layers of encryption and bounced through a volunteer-run relay network. Simultaneously, the hidden service advertises its existence through introduction points. A rendezvous point facilitates a connection without either party knowing the other's true IP address. This complex dance makes traffic extremely difficult to trace.
- Anonymity for Users: Your internet service provider cannot see you are visiting an .onion site.
- Resilience for Services: Hosts can operate without revealing their server's physical location.
- Censorship Resistance: The decentralized nature makes these links very hard to block permanently.
Common Uses and Misconceptions
While .onion links are often associated with illicit marketplaces, their legitimate uses are vast and critical. Many organizations use them to offer secure, anonymous access to their public services.
- News Organizations: Outlets like The New York Times and BBC run .onion mirrors for readers in censored regions.
- Privacy Tools: Secure email services, search engines like DuckDuckGo, and software projects often provide .onion portals.
- Whistleblower Platforms: Secure drop sites for leaking information frequently operate as hidden services.
FAQs About .onion Links
Is it illegal to access the Tor network or .onion sites?
No. Using Tor and accessing .onion links is legal in most countries. It is a tool for privacy, much like a VPN. However, illegal activities conducted on any network remain illegal.
Are .onion links completely anonymous and safe?
While the technology provides strong anonymity, it is not foolproof. User errors, malware, or compromised servers can pose risks. Always exercise caution and keep software updated.
Can I search for .onion links on Google?
Standard search engines do not index most .onion sites. You need to use dedicated directories hosted on the Tor network itself or rely on community recommendations from trusted sources.
Ultimately, .onion links represent a fundamental technology for digital privacy and free speech. They empower individuals to access information and communicate without fear of surveillance or reprisal, carving out a crucial space for freedom in an increasingly monitored digital world.