The most effective defense against dark web threats is preventing your sensitive data and credentials from being compromised in the first place. Professional threat intelligence services handle the technical and legal complexities while providing actionable insights for your security team. The threat landscape is constantly evolving as criminals develop new techniques and share knowledge through these hidden channels, with underground forum breach data sharing increasing by 43% in 2024. Dark web users have varied intentions, from privacy protection to illegal activities. For the dark web, the focus shifts to threat intelligence—monitoring for stolen data, credentials, and emerging attack methods.
Results are filtered to preserve anonymity, avoid illegal content in some engines, and often include metadata such as site age, uptime, and indexing date. These search engines are mostly employed in the fields of research, detection work, and intelligence where access to dark web sites is an absolute necessity. An onion search engine is at the forefront in this matter, enabling users to find .onion domains that are not visible on the normal internet.
The internet is a vast ecosystem, with its most visible layer being the surface web we use daily. Beneath this lies the deep web, consisting of unindexed pages like private databases and subscription services. Deeper still is the dark web, a small, intentionally hidden segment that requires specific software to access. While often associated with illicit activity, it also serves as a crucial tool for whistleblowers, journalists, and citizens under oppressive regimes seeking privacy and uncensored communication.
Accessing Dark Web
That often includes mirrors, abandoned services, spam pages, and low-quality results that curated tools suppress. Torch is widely referenced as a long-running Tor search engine, even though it offers limited public detail about how it indexes content. Private open-web research inside Tor is the real advantage, not hidden-service indexing.
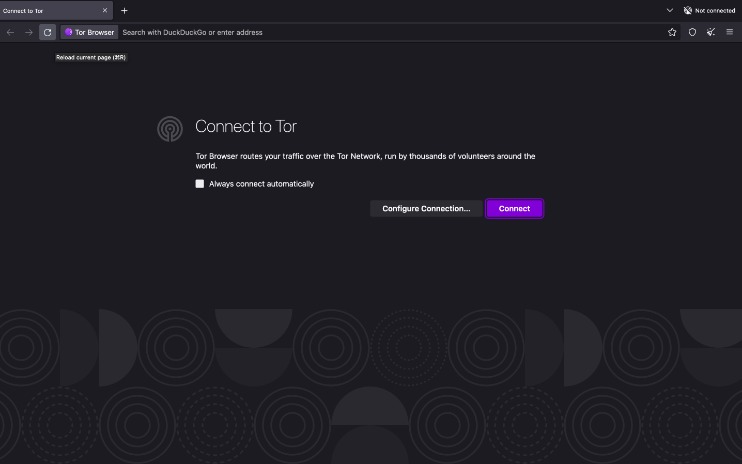
Accessing the dark web is technically straightforward but comes with significant caveats. It is not done through standard browsers like Chrome or Firefox. Instead, it relies on overlay networks, the most famous being Tor (The Onion Router). The process of accessing the dark web involves downloading and installing the Tor Browser, which routes your traffic through multiple encrypted layers, anonymizing your location and usage.
Essential Tools and Precautions
Before even considering accessing the dark web, understanding the tools and risks is paramount.
- Tor Browser: The primary gateway. It is a modified Firefox browser that connects to the Tor network.
- VPN (Virtual Private Network): Many experts recommend using a reputable VPN before connecting to Tor for an added layer of security.
- Security Mindset: Disable scripts, avoid downloading files, and never use personal information. Assume you are being watched.
- Legal Risks: Navigating to illegal marketplaces or content is a crime in most jurisdictions.
What You Might Encounter

The experience of accessing the dark web can be disorienting. Websites use .onion addresses and are often slow due to the routing. Content ranges from legitimate to highly dangerous:
- Almost 99% of web content is thought to evade search engines.
- Other risks include the security of investigators and their machines.
- The dark web, on the other hand, uses encryption software to provide even greater security.
- Accessing the dark web is generally legal, but many activities there are not.
- Search engines like Google can’t access the Deep Web and Dark Web simply because their content is not indexed.
- Stay ahead of impending threat trends, dark web or otherwise, by watching our 2022 threat report findings webinar.
- Whistleblower drop sites (e.g., SecureDrop).
- Privacy-focused forums and email services.
- Illicit marketplaces for drugs, weapons, and stolen data.
- Disturbing and illegal content.
- Although the Dark Web is often used for illegal activities, it’s not illegal to access it in many countries.
- Some surface websites—such as Facebook—even have official dark web versions.
- The layout focuses on giving users working, legitimate results, even if that means having a smaller index compared to broader engines.
- Listen to expert conversations and insights on cybersecurity trends, threats and best practices.
FAQs on Accessing the Dark Web
Is accessing the dark web illegal?
No, the act of accessing the dark web itself is not illegal in most free countries. It is a tool. However, many activities conducted on it are illegal, and simply visiting certain sites may be a crime.

Can I be tracked?
While Tor provides strong anonymity, it is not infallible. Sophisticated adversaries or user error can compromise your identity. The security of accessing the dark web is not absolute.
Why would a regular person use it?
For enhanced privacy in an era of mass surveillance, to access news censored in their country, or to communicate sensitive information securely.
In conclusion, accessing the dark web is a double-edged sword. It represents both the pinnacle of private, anonymous communication and a shadowy haven for criminal enterprise. Anyone venturing into it must be technically prepared, legally aware, and exercise extreme caution at every step. The allure of the hidden internet is powerful, but the risks are very real.