The digital landscape extends far beyond the surface web indexed by common search engines. Beneath lies a vast, encrypted network known as the darknet, a segment of the deep web intentionally hidden and requiring specific software to access darknet markets and other hidden services. These markets, operating as digital bazaars, have become infamous for facilitating trade in illicit goods, though they also host legal activities where anonymity is paramount.
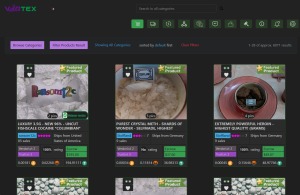
Tor66 combines traditional search with a categorized directory of .onion sites. In June 2015 the European Monitoring Centre for Drugs and Drug Addiction (EMCDDA) produced a report citing difficulties controlling virtual market places via darknet markets, social media and mobile apps. Personally identifying information, financial information like credit card and bank account information, and medical data from medical data breaches is bought and sold, mostly in darknet markets but also in other black markets. Some criminal internet forums such as the defunct Tor Carding Forum and the Russian Anonymous Marketplace function as markets with trusted members providing escrow services, and users engaging in off-forum messaging. Uptime and comparison services provide sources of information about active markets as well as suspected scams and law enforcement activity. Following on from the model developed by Silk Road, contemporary markets are characterized by their use of darknet anonymized access (typically Tor), Bitcoin or Monero payment with escrow services, and eBay-like vendor feedback systems.
- In the summer of 2017, a team of cyber cops from three countries successfully shut down AlphaBay, the dark web’s largest source of contraband, sending shudders throughout the network.
- As a result, “The quality of search varies widely, and a lot of material is outdated.”
- DWMs are accessed through darknet browsers supporting the onion routing protocol (e.g., Tor), which provides anonymous communication connections35.
- Traditional markets are regulated by governments, and products sold are subject to laws and regulations.
- In April of 2023 there were about 2.7 million daily visitors to the dark web, and research shows that 56.8% of the content on the dark web is illegal in some way.
Access Darknet Markets
As market operators, it is necessary to apply appropriate mechanisms to protect user accounts, which can help users avoid potential account loss, theft, scams, etc. Compared with DDoS protection services on the clear web, EndGame can be deployed locally rather than hosted on a third party (like Cloudflare), which fits well with the privacy requirements of market operators. In practice, some markets have very restrictive thresholds, making it very challenging to obtain data for the entire market. However, markets with open circles do not mention any guidance about what users should do if a bug is discovered. We have noticed that some markets have canaries that are out of date, but operators usually update them after a few days. We also noticed that three markets (ASAP Market, Nemesis Market, Chinese Exchange Market) allow access to product pages even if the user is not logged in or registered.
To access darknet markets, one must first navigate the technical barriers that define this space. The primary gateway is the Tor network, which anonymizes traffic by routing it through multiple volunteer-operated servers. Downloading the Tor Browser is the essential first step, providing the necessary conduit to .onion addresses, the unique identifiers for darknet sites. This process is the foundational act required to access darknet markets and represents the initial layer of user obfuscation.

The Precautions and Pitfalls
Merely knowing how to access darknet markets is a far cry from doing so safely or ethically. The environment is rife with scams, malware, and law enforcement operations. Users often employ additional encryption tools, like PGP for communication, and exclusively use cryptocurrencies such as Bitcoin or Monero. The act to access darknet markets is inherently risky, exposing individuals to criminal prosecution, financial loss, and dangerous products. The anonymity that attracts users is also a shield for malicious actors.
The Ecosystem and Its Implications
- After a breach, security teams need to understand what data was stolen and where it went.
- The dark web cannot rely solely on crawling in the same way the surface web is — indexes are sometimes added to dark web search engines manually by the site operator, too.
- It is essential to understand the differences between these two markets, as they operate differently and have their respective advantages and disadvantages.
- The horizontal bars represent each market lifetime, i.e., the time when the market becomes active until its closure, and is colored according to the market’s monthly trading volume in USD.
- Previous studies have mainly focused on social aspects, including analysis of products sold, emerging criminal patterns, criminal ecosystems, and key actors 14, 19, 20, 23, 24, 34.
Once inside, the ecosystem is complex. Vendors build reputations on feedback systems, much like surface web e-commerce, but for contraband. The persistent drive to access darknet markets for illegal commodities presents a continuous challenge for global law enforcement, leading to a cyclical pattern of market takedowns and subsequent re-emergence. This cat-and-mouse game underscores the resilient, if illicit, demand that fuels the creation of new platforms.
In conclusion, the knowledge of how to access darknet markets is a double-edged sword, representing both a technical understanding of privacy networks and a potential gateway to significant legal peril. The infrastructure that allows one to access darknet markets exists for legitimate privacy reasons, but its predominant notoriety stems from its misuse, highlighting the ongoing tension between anonymity, freedom, and criminality in the digital age.