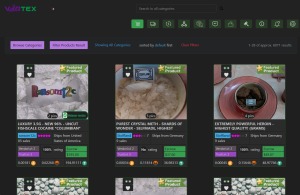
The digital shadows have grown longer and more intricate. By 2026, the concept of a working darknet market has evolved beyond simple illicit bazaars into a complex ecosystem defined by relentless adaptation, sophisticated technology, and a paradoxical focus on user experience and security. These platforms no longer merely exist; they are engineered to persist, leveraging decentralized architectures and emerging cryptographic techniques to stay operational amidst global law enforcement pressure.
- According to court documents, Helix was one of the most popular mixing services on the darknet and was highly sought after by online drug dealers seeking to launder their illicit profits.
- Besides Hydra operators, other DNM administrators faced criminal prosecution in 2024.
- The encryption and operational security implemented by marketplace operators may have been “rarely as convincing as previously advertised,” as one German legal analysis noted.
- Unlike manual search, they access private sources and provide real-time alerts.
- While these hidden networks can be used for legitimate purposes, they are equally significant as vectors for cybercrime and illicit activities.
Get the insights you need to make informed, actionable decisions—and stop threats before they strike. We break news and interview those that matter in the fast-changing field of cybersecurity. Stay ahead of the ever-evolving threat landscape with our daily snapshot of your most pressing risks.
Instead, it focuses on publishing stories and holding powerful institutions accountable. Use your common sense to steer clear of online scams and illegal activity. It’s been around for many years and helps users navigate the dark web by curating links to various resources. Concerns about how Meta treats user data have led many people to delete their Facebook profiles or at least limit their social media presence. DuckDuckGo is a privacy-focused search engine that works as Tor browser’s primary search engine.
2026 Working Darknet Market
The defining feature of a successful 2026 working darknet market is its infrastructure. Centralized servers, the Achilles' heel of past markets like Silk Road, are now largely obsolete. Instead, resilience is built on:
- Decentralized Hosting: Utilizing peer-to-peer networks, decentralized file storage, and even blockchain-based front-ends to eliminate single points of failure.
- AI-Powered Security: Automated systems that monitor for infiltration attempts, scan for malware in vendor listings, and detect anomalous user behavior.
- Quantum-Resistant Cryptography: With quantum computing on the horizon, forward-thinking markets are implementing encryption algorithms designed to withstand future decryption threats.
Economic and Operational Models
The economy within a 2026 working darknet market has matured. Cryptocurrency remains king, but with significant twists. Privacy coins with enhanced protocols are standard, and some markets have integrated cross-chain atomic swaps to obscure financial trails further. Vendor reputations are no longer just based on reviews; they are built on verifiable, on-chain transaction histories that are cryptographically secured and impossible to forge.
Operational security (OpSec) for users and vendors is deeply embedded into the market's design. Mandatory PGP encryption, integrated Tor-over-VPN guidance, and automated transaction timers are standard features. The user interface of these platforms often rivals that of legitimate e-commerce sites, creating a jarring contrast between the sleek front-end and the illicit nature of the goods traded.
Challenges and Countermeasures
Despite their sophistication, no 2026 working darknet market is impervious. Law enforcement agencies have escalated their tactics in response, employing advanced network analysis, infiltrating market administration, and deploying blockchain forensic tools at scale. This has led to a continuous cycle of innovation and disruption, where markets frequently undergo "security migrations" or spontaneously fragment into smaller, invite-only cells to maintain their status as a working entity.

FAQs on the 2026 Darknet Landscape
Q: How do users find a legitimate 2026 working darknet market?
A: Access is increasingly gated through private forums and invitation-only channels on encrypted messaging apps. Public directories are considered untrustworthy and high-risk.
- Tor66 blends a traditional search engine with a categorized directory of onion sites.
- To secure against these risks, organizations invest in robust cybersecurity strategies, conduct regular security assessments, and educate employees to recognize and mitigate threats.
- Some vendors offer “access as a service” where they maintain persistent access to compromised networks and sell it repeatedly to different buyers.
- During sentencing, District Judge Colleen McMahon told Lin that Incognito Market was “a business that made him a drug kingpin," and that this was the “most serious drug crime I have ever been confronted with in 27.5 years.”
- Third, the ransomware economy has created a robust market for corporate data.
Q: What is the biggest risk for users?
A> Beyond legal repercussions, the threat of exit scams remains, alongside sophisticated phishing mirrors and the ever-present risk of dealing with undercover law enforcement posing as vendors.
Q: Have the types of goods changed?
A> While traditional illicit goods persist, there is a noted rise in digital contraband: stolen datasets, zero-day exploits, AI-generated disinformation services, and forged digital identity packages.
In conclusion, the 2026 working darknet market represents a high-stakes arena of technological one-upmanship. It is a resilient, adaptive entity shaped by the dual forces of criminal innovation and relentless pursuit, existing in a state of perpetual flux deep within the hidden layers of the internet.