In the shadowed corridors of the digital world, a specific type of threat carries a potent and unsettling allure. This is the realm of the 0day onion, a term that layers two distinct concepts of cybersecurity and privacy into a single, formidable idea. It represents not just an unknown software vulnerability, but the clandestine ecosystem where such flaws are traded, hidden beneath the anonymity of the Tor network.
0day Onion
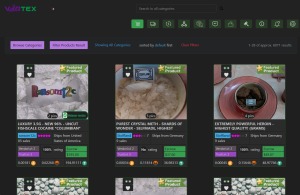
The "0day" component refers to a software vulnerability that is unknown to the vendor, leaving zero days for a patch to be developed. These flaws are highly prized commodities in cyber arms markets. When such an exploit is bundled and sold on a hidden service—an ".onion" site—it transforms into a 0day onion. This marketplace operates with a degree of insulation from conventional law enforcement, accessible only through specialized browsers and often protected by complex authentication and cryptocurrency payments.

A newly discovered 0day exploit targeting the Tor browser bundle or the underlying network protocol could potentially de-anonymize users or compromise hidden services before developers have a chance to issue a patch. Access the complete 0day.today archive featuring nearly 30 years of historical exploits and vulnerability research from the legendary milw0rm underground security community. Long-day onions tend to have a more pungent flavor and thicker skins due to the cooler temperatures, making these varieties generally better for storage than fresh eating. We consider vulnerability a zero-day when there is no solution provided from software vendor and the vulnerability is being actively exploited by malicious actors. However, widespread adoption of 0day onion solutions faces regulatory and legal challenges.
When users connect to a hidden service, their communication is encrypted in layers and routed through multiple nodes, each decrypting a layer before passing it along. These vulnerabilities can be leveraged to inject malware, steal data, or conduct large-scale attacks on targeted systems. Dive into the enigmatic world of the darknet, where encrypted communications and hidden enclaves define a clandestine society. Companies like the French hacking firm Vupen, by contrast, argue that it sells zero-day vulnerabilities only to NATO governments or allies.
The Layered Economy
- EDB and 0day.today both contain tens of thousands of exploits, and although there is a good amount of overlap between the projects, they each offer their own unique exploits.
- Out of all the forums launched at the same time as CryptBB, this site is the only recognized service still available.
- Automate your reconnaissance process with AttackSurfaceMapper, a tool for mapping and analyzing network attack surfaces.
- The landscape of cybersecurity is continually evolving, presenting both opportunities and significant challenges for law enforcement and regulatory bodies.
- The Onion Router (Tor) network provides a powerful framework for anonymity by routing a user’s internet traffic through a series of volunteer-operated servers, encrypting it in layers at each step.
The trade of a 0day onion follows a sophisticated, multi-layered economy. Brokers and vendors communicate through encrypted channels, with the final transaction occurring on a hidden forum or auction site. The value of a 0day onion is determined by its impact, scope, and longevity—a flaw in a ubiquitous system like a major operating system commands a far higher price than one in a niche application. This economy fuels both state-sponsored espionage and financially motivated criminal enterprises.
Implications and Defense
The existence of these markets presents a profound challenge. A 0day onion in the wrong hands can lead to catastrophic data breaches, critical infrastructure attacks, or persistent surveillance campaigns. Defending against an attack leveraging a true 0day is exceptionally difficult, as there is no signature or patch available. Security teams must therefore rely on behavioral analysis, network segmentation, and stringent application control to limit potential blast radius, always operating under the assumption that an unseen vulnerability could be exploited at any moment.
Ultimately, the 0day onion symbolizes the ongoing asymmetric battle in cybersecurity. It highlights a world where offensive capabilities can be developed and traded in near-total secrecy, forcing defenders to constantly adapt their strategies in a landscape where the most dangerous threats are, by definition, the ones they have not yet seen.