The internet is often compared to an iceberg, with the familiar surface web representing the visible tip. Beneath lies the deep web, consisting of unindexed private databases and pages. Deeper still exists a distinct layer known for its anonymity and notoriety: the realm of .onion services, commonly called the dark web. This network, accessible only through specialized software, operates on a foundation of encrypted connections and hidden locations, creating an environment unlike any other on the internet.
onion Dark Web
- The Tor browser is carefully configured for privacy, and adding extensions (even secure ones) can break anonymity or leak information about you.
- What’s illegal is your actions on the dark web such as buying illicit goods or downloading child abuse material.
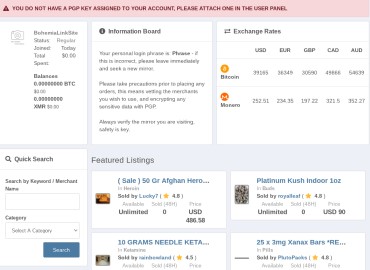
- Vortex is an anonymous, responsive, and user-friendly darknet marketplace with an excellent user experience.
- The open-source setup also allows analysts to adapt it for their own research systems.
The dark web is often portrayed as vast and mysterious, implying that there is a large number of onion sites on Tor, but this is not what we find. According to Wikipedia, the dark web can be described as any web content that requires specific software, configurations, or authorization to access. To provide authenticated, end-to-end access for users in censored regions or to reduce exit-node risks.
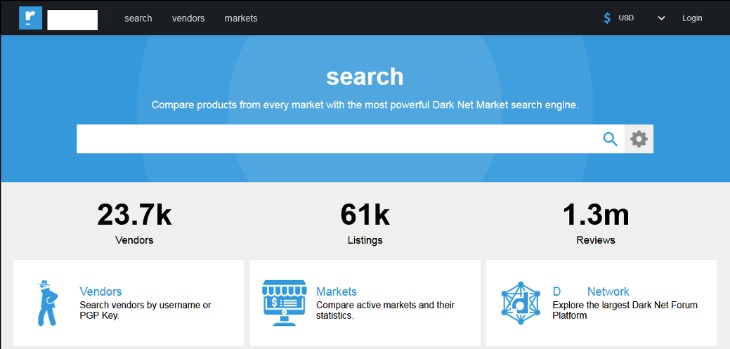
For an unknown reason, there are thousands of variations for the onion domain for this site using different placements of a non-printing character in the URL. One of the largest sources of duplication was 5,941 duplicates of the Deep Dot Web onion site. The approach was a web crawler (“spider”) that uses a Tor browser simulator. For years, Recorded Future has collected targeted dark web content that is relevant to our clients.
The publicizing of Snowden’s actions led to a global spike of interest in Tor and a resulting rapid expansion of the network’s user base. National Security Agency (NSA) contractor Edward Snowden, who was concerned about the extent of government surveillance, used Tor to coordinate with journalists on leaking 1.5 million classified government documents. Not all mass thefts of data facilitated by the dark web have been motivated by money. Credit card and social security numbers are routinely purchased, as are passwords for e-mail accounts—sometimes en masse.
At the core of this ecosystem is the .onion top-level domain. Unlike conventional domains, these addresses are not registered through a central authority but are generated as cryptographic hashes of a service's public key. This makes .onion sites inherently hidden; their location and ownership are obscured by design. Access requires a gateway, most famously the Tor browser, which routes traffic through multiple volunteer relays, encrypting it each step of the way to conceal a user's origin and destination.
A Dual-Natured Environment

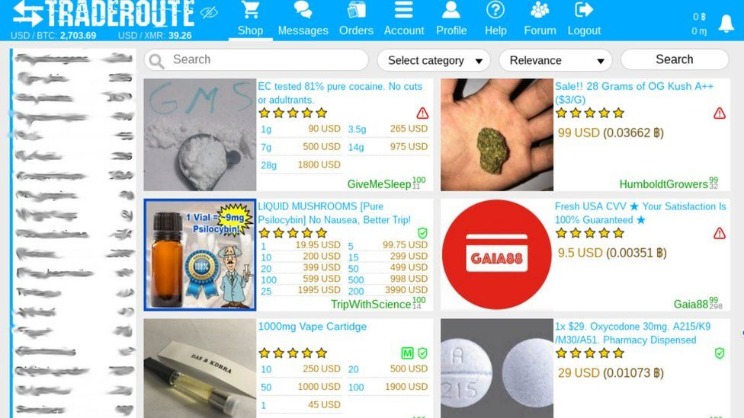
The architecture of the .onion dark web provides powerful tools for both liberation and criminal activity. It is a vital refuge for whistleblowers, journalists in oppressive regimes, and individuals seeking privacy from surveillance. Activist communities and secure drop services often operate here. Conversely, the same anonymity shields illicit marketplaces, hacking forums, and other illegal operations. This duality is the defining characteristic of the network.
Navigating the Hidden Layers
- When you access Dark Web Academy via our .onion site, your IP address is never exposed to our servers, and all traffic is encrypted end-to-end within the Tor network.
- That’s right—threat actors have their very own court system, along with codes of conduct to follow to minimize the chances of landing there themselves.
- In pop culture, the “Dark Net” became routinely depicted as an online demimonde—a nightmare vision of the dark side of the Internet.
- Isn’t that the whole point of onion services?
- Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity.
- The Tor browser is configured to automatically connect to the Tor network (also known as the onion network) as soon as you load it, and you can instantly open regular and onion links in it.
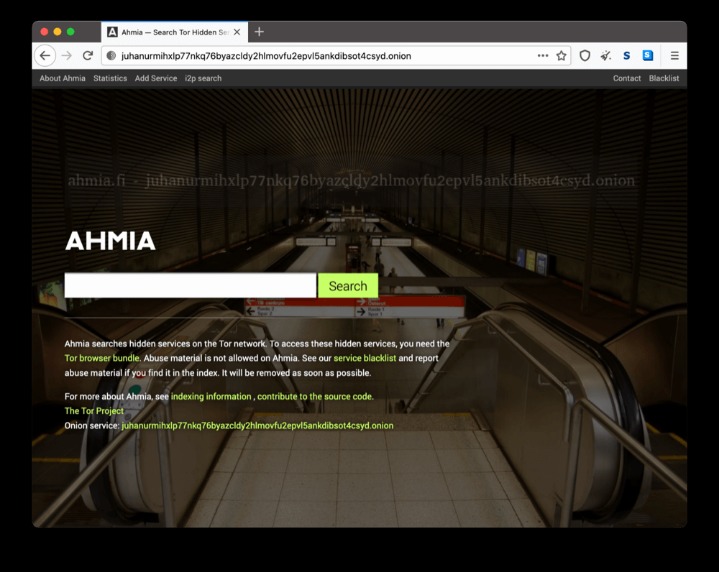
Finding resources on the .onion dark web is challenging, as traditional search engines do not index these pages. Users rely on curated directories, community wikis, and word-of-mouth shared on specialized forums. The transient nature of .onion sites is also notable; addresses frequently change, and sites can disappear without warning, a phenomenon often referred to as "link rot."
Ultimately, the .onion dark web is a technological reality reflecting the full spectrum of human behavior. It is neither purely a criminal haven nor an unfettered utopia for free speech, but a complex and controversial space made possible by the rigorous application of cryptography and peer-to-peer networking principles. Its existence continues to provoke significant debate about privacy, security, and the boundaries of online freedom.